Copyright © 2003 Thomas M. Eastep, Simon Mater
Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or any later version published by the Free Software Foundation; with no Invariant Sections, with no Front-Cover, and with no Back-Cover Texts. A copy of the license is included in the section entitled “GNU Free Documentation License”.
2003-02-04
Table of Contents
OpenVPN is a robust and highly configurable VPN (Virtual Private Network) daemon which can be used to securely link two or more private networks using an encrypted tunnel over the internet. OpenVPN is an Open Source project and is licensed under the GPL. OpenVPN can be downloaded from http://openvpn.sourceforge.net/.
OpenVPN support was added to Shorewall in version 1.3.14.
Suppose that we have the following situation:
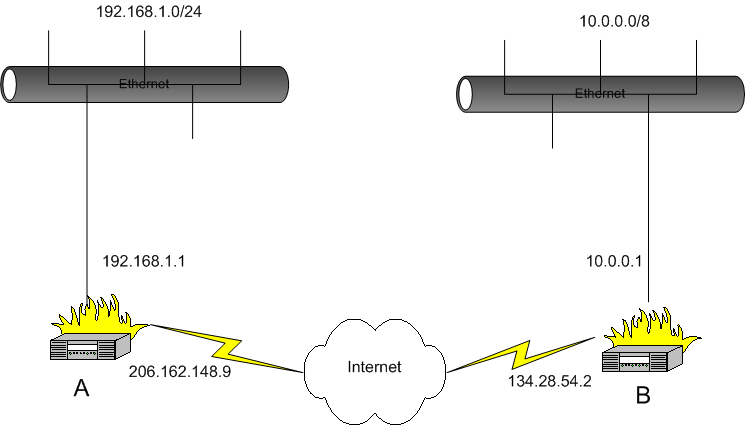
We want systems in the 192.168.1.0/24 subnetwork to be able to communicate with the systems in the 10.0.0.0/8 network. This is accomplished through use of the /etc/shorewall/tunnels file and the /etc/shorewall/policy file and OpenVPN.
While it was possible to use the Shorewall start and stop script to start and stop OpenVPN, I decided to use the init script of OpenVPN to start and stop it.
On each firewall, you will need to declare a zone to represent the remote subnet. We'll assume that this zone is called “vpn” and declare it in /etc/shorewall/zones on both systems as follows.
On system A, the 10.0.0.0/8 will comprise the vpn zone. In /etc/shorewall/interfaces:
In /etc/shorewall/tunnels on system A, we need the following:
This entry in /etc/shorewall/tunnels opens the firewall so that OpenVPN traffic on the default port 5000/udp will be accepted to/from the remote gateway. If you change the port used by OpenVPN to 7777, you can define /etc/shorewall/tunnels like this:
This is the OpenVPN config on system A:
dev tun local 206.162.148.9 remote 134.28.54.2 ifconfig 192.168.99.1 192.168.99.2 up ./route-a.up tls-server dh dh1024.pem ca ca.crt cert my-a.crt key my-a.key comp-lzo verb 5 |
Similarly, On system B the 192.168.1.0/24 subnet will comprise the vpn zone. In /etc/shorewall/interfaces:
In /etc/shorewall/tunnels on system B, we have:
And in the OpenVPN config on system B:
dev tun local 134.28.54.2 remote 206.162.148.9 ifconfig 192.168.99.2 192.168.99.1 up ./route-b.up tls-client ca ca.crt cert my-b.crt key my-b.key comp-lzo verb 5 |
You will need to allow traffic between the “vpn” zone and the “loc” zone on both systems -- if you simply want to admit all traffic in both directions, you can use the policy file:
On both systems, restart Shorewall and start OpenVPN. The systems in the two masqueraded subnetworks can now talk to each other.